The Day the Internet Almost Died (And Nobody Knew)
There’s a developer somewhere—let’s call him Andres—sitting at his desk in late March 2024, debugging SSH connections on a beta Linux system. Something’s wrong. The login is slow. Just half a second too slow.
Most people would have ignored it. A coffee break. A quick restart. Move on.
Andres didn’t ignore it.
That curiosity—that obsessive attention to a 500-millisecond delay—saved the internet.
The Invisible Foundation
Picture this: buried deep in the digital infrastructure that runs our world, there’s code written by volunteers. Unpaid. Unrecognized. Working night shifts after their day jobs, maintaining the invisible foundations of civilization.
One of these pieces is XZ Utils—a compression tool so fundamental that it’s embedded in nearly every Linux system on Earth. Every server. Every cloud instance. Every digital heartbeat of the modern world.
It was maintained by one man: Lasse Collin. Alone. Unpaid. For years.
Enter the White Knight
Late 2021. Lasse is drowning. Bug reports pile up. Users demand features. The pressure is relentless. Then salvation arrives in the form of Jia Tan—a helpful contributor who starts fixing bugs, adding features, easing the burden.
Over two years, Tan becomes indispensable. Trusted. Essential.
The community begins pressuring Lasse to give Tan more control. Emails arrive—seemingly from journalists, from other developers—all asking the same question: “Why haven’t you made Tan a maintainer yet?”
It’s a social engineering masterpiece. Subtle. Patient. Perfectly orchestrated.
Tan never gets full maintainer status, but he gets something almost as good: control over the release process.
The Trojan Horse
February 2024. Two releases of XZ Utils slip out. Not through the public Git repository—those are clean—but through separate tarballs sent directly to distributions. Fedora. Debian testing. The bleeding edge systems that would eventually flow downstream to millions of servers.
The code is brilliant. Malicious. Almost invisible.
It works normally. XZ compresses and decompresses files just fine. There’s a slight slowdown—nothing obvious. Just enough CPU overhead that you’d blame it on background processes or an aging system.
But hidden inside is a backdoor. A master key to the internet.
When a specially crafted SSH connection arrives—a connection that only the attacker knows how to create—the system grants access. No password. No keys. No authentication.
Remote code execution. Full control. Silent. Invisible.
The Scope of the Almost-Catastrophe
Think about what this means:
Every cloud server running the compromised version—accessible.
Every cryptocurrency wallet—ready to be emptied.
Every database—open for reading, modification, destruction.
Every encrypted communication—compromised at the source.
Every secret—exposed.
This wasn’t some theoretical vulnerability. The backdoor was already deployed. It was in stable distributions. It was spreading. In weeks—maybe days—it would have reached production systems worldwide.
The only thing preventing global digital catastrophe was that it hadn’t quite made it to stable releases yet. It was in Fedora 41 (beta) and Debian testing. The stable versions that power production servers worldwide were scheduled to receive it in their next update cycle.
April 2024 was going to be the month the internet broke. Nobody knew.
500 Milliseconds of Luck
March 29, 2024. Andres Freund, a Microsoft engineer and PostgreSQL developer, is testing something on a Debian system. He notices SSH is slow. Half a second slow.
He doesn’t ignore it.
He starts digging. Profiling CPU usage. Watching system calls. Following the threads of execution through the system. He discovers something impossible: the SSH daemon (sshd) is calling functions from liblzma—the compression library from XZ Utils.
Why would SSH authentication need compression functions?
He goes deeper. Reverse engineers. Finds obfuscated code. Binary blobs disguised as test files. A multi-stage payload that only activates under specific conditions.
On March 29, 2024, he sends an email to a security mailing list with a subject line that could have been titled “I accidentally saved the internet.”
The Response
Within hours, emergency patches flood out. Distributions roll back XZ Utils. CVE-2024-3094 becomes one of the most critical vulnerabilities ever discovered. Security researchers worldwide start dissecting the code.
What they find is terrifying:
- Two years of planning: Tan had been building trust, contributing genuine improvements, establishing credibility
- Social engineering: Fake accounts pressuring the maintainer to grant access
- Sophisticated obfuscation: Multi-stage payloads, conditional activation, cleanup routines that made the installed package look normal
- Nation-state level resources: The patience, technical sophistication, and coordination point to a well-funded, professional operation
”Jia Tan” disappears. The accounts go silent. Investigators can’t determine who was behind the name. China? Russia? North Korea? The clues point everywhere and nowhere—intentionally.
The Uncomfortable Truth
Here’s what keeps security researchers awake at night:
The entire digital infrastructure of modern civilization rests on tools maintained by volunteers. Unpaid individuals working in their spare time, often alone, holding together the foundation of trillion-dollar industries.
Lasse Collin, the maintainer of XZ Utils, was burning out. Drowning in work. Desperate for help. When that help arrived in the form of Jia Tan, it felt like salvation.
But it was a trap.
And it almost worked.
XKCD has a famous comic (#2347: “Dependency”) showing the entire modern digital infrastructure balanced precariously on a tiny block labeled “a project some random person in Nebraska has been thanklessly maintaining since 2003.”
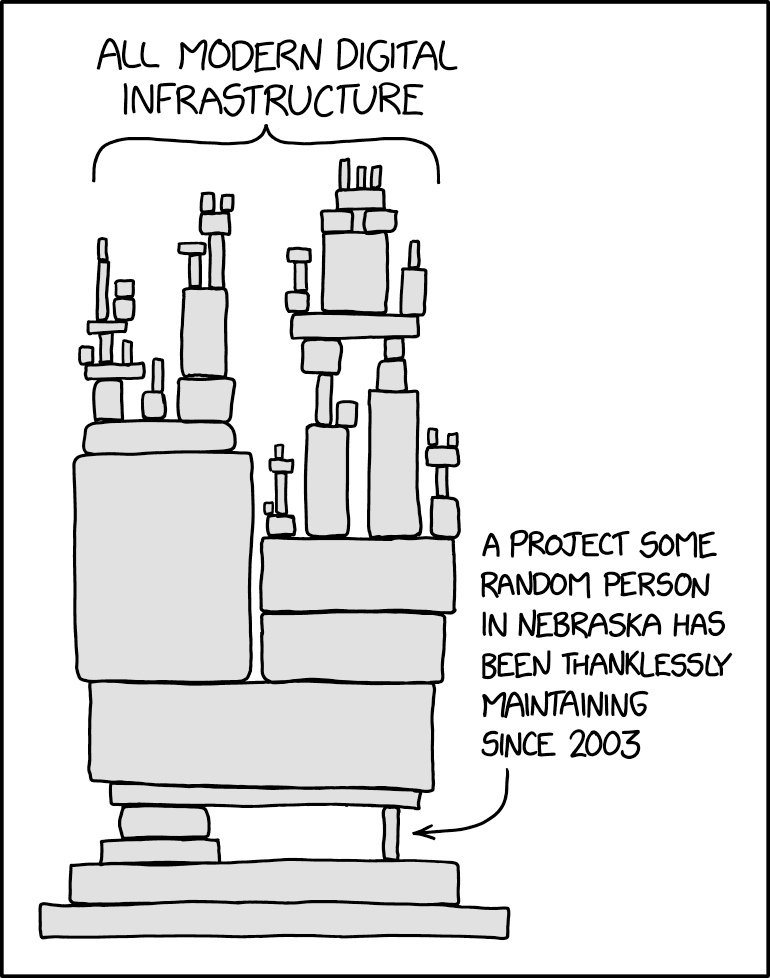
That’s not a joke. That’s reality.
What We Learned (And Didn’t)
The XZ Utils backdoor was discovered. Fixed. Removed. CVE-2024-3094 is now a cautionary tale in security textbooks.
But the underlying problem remains:
- Critical infrastructure still maintained by unpaid volunteers
- Burnout leading to security compromises
- Sophisticated attackers targeting the weakest links
- No sustainable funding model for open-source fundamentals
Linus’s Law states: “Given enough eyeballs, all bugs are shallow.” But when critical tools are maintained by one person, there aren’t enough eyeballs. The law breaks down.
The Hero Nobody Knows
Andres Freund didn’t set out to save the internet. He was just debugging a slow SSH connection. His name should be in history books next to people who prevented nuclear disasters or caught assassins before they struck.
Instead, most people have never heard of him.
Most people didn’t know the internet almost died in spring 2024.
But it did. It came within weeks—maybe days—of catastrophe.
And it was saved by one person who refused to ignore a 500-millisecond delay.
The Epilogue
Today, XZ Utils is secure again. Lasse Collin still maintains it, though with much more scrutiny and support now. The Linux community has implemented additional safeguards. Security researchers regularly audit critical utilities.
But somewhere, right now, there’s another critical piece of infrastructure maintained by an overworked volunteer. Another “Jia Tan” gaining trust. Another patient, sophisticated attack in progress.
The next one might not be caught by someone debugging a slow login.
The next one might succeed.
What You Can Do
If you work at a company that depends on open source:
- Pay the maintainers - Don’t just donate. Directly fund critical projects.
- Provide resources - Offer security audits, infrastructure, development support.
- Don’t just take - Contribute back. Review code. Share the maintenance burden.
If you’re a developer:
- Review your dependencies - Know what your code depends on.
- Support maintainers - File good bug reports. Contribute patches. Say thank you.
- Be vigilant - If something seems off, investigate. Trust your instincts.
The internet runs on trust, volunteers, and luck.
We got lucky this time.
We might not be so lucky next time.
Technical Details
For those interested in the specifics:
- CVE: CVE-2024-3094
- Affected versions: XZ Utils 5.6.0 and 5.6.1
- Attack vector: Modified liblzma library intercepting SSH authentication
- Discovery date: March 29, 2024
- Discoverer: Andres Freund (Microsoft/PostgreSQL)
- Timeline: ~2 years of preparation, stopped weeks before widespread deployment
Further Reading
- OpenSSF Blog: XZ Backdoor CVE-2024-3094
- Original discovery post by Andres Freund
- Detailed technical analysis by security researchers
- The Wired article on Jia Tan’s identity investigation
- Veritasium’s YouTube video explaining the incident
Sometimes the most important stories are the ones where nothing happened—because someone was paying attention.